Zero Trust Security Model Demystified: A Modern Blueprint for Unbreakable Cyber Defense
The digital ecosystem has expanded far beyond traditional office networks, transforming how organizations operate and how users access information. Employees work remotely, data is stored in cloud platforms, and applications run across multiple environments. The Zero Trust Security Model changes this outdated approach by removing automatic trust from digital environments. It introduces a system where every user, device, and connection must prove legitimacy continuously.Unfortunately, attackers have learned to exploit this assumption through phishing, credential theft, and malware intrusions. Once they gain access, they often move laterally without detection.
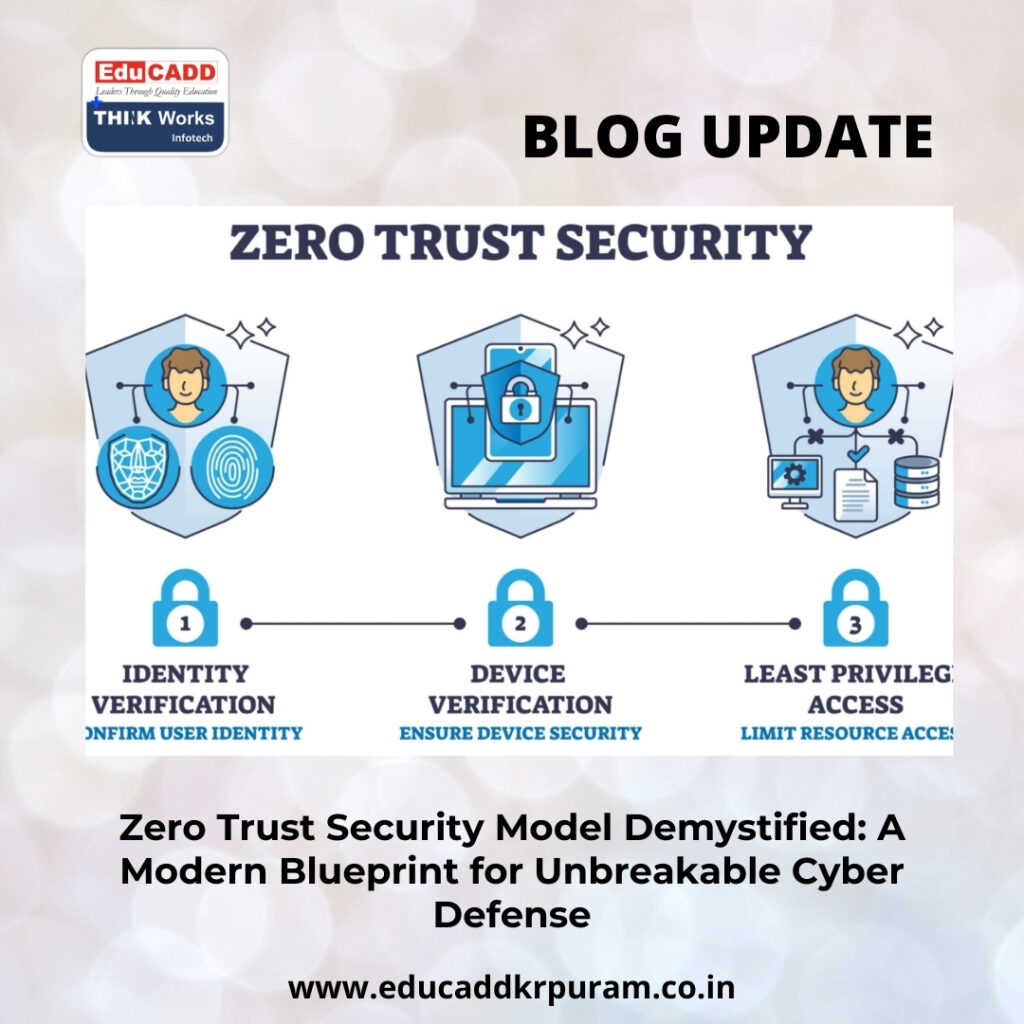
Zero Trust Security Model
While this digital evolution increases flexibility and productivity, it also exposes systems to advanced cyber threats. Older security frameworks depended heavily on perimeter defenses, assuming that anyone inside the network could be trusted. This model strengthens cybersecurity by enforcing strict identity verification, monitoring behavior in real time, and limiting access privileges. Organizations adopting this approach gain stronger protection against breaches while maintaining operational efficiency in today’s interconnected world.
1. The Core Philosophy Driving Zero Trust Security
At the heart of the Zero Trust Security Model lies a simple yet powerful philosophy: trust must always be earned and never assumed. Traditional systems allowed users to access multiple resources after a single authentication step, creating opportunities for attackers to exploit internal vulnerabilities. Zero Trust eliminates this risk by requiring verification for every request, regardless of the user’s location within or outside the network. Each interaction must pass authentication and authorization checks based on identity credentials, device safety status, and contextual information. Trust becomes dynamic rather than permanent, meaning access permissions are reassessed continuously. This method significantly reduces the chances of unauthorized users moving freely across digital environments.
2. Why Perimeter-Based Security Cannot Protect Modern Systems
Perimeter-focused cybersecurity strategies were effective when corporate data resided within centralized infrastructures. Firewalls and intrusion detection tools formed strong outer barriers that prevented unauthorized access. However, modern workplaces rely on cloud services, mobile devices, and remote connectivity, which dissolve clear network boundaries. Attackers now bypass perimeter defenses using stolen passwords or infected endpoints. Once inside, traditional systems often fail to detect malicious activity. The Zero Trust Security Model addresses this vulnerability by shifting security focus from location-based trust to identity-centered validation. Protection mechanisms follow users and devices wherever they connect, ensuring consistent security across diverse environments.
3. Foundational Principles That Shape Zero Trust Architecture
Several essential principles guide the implementation of the Zero Trust Security Model and ensure comprehensive digital protection.
• Continuous validation confirms user identities throughout active sessions.
• Strict access policies ensure users interact only with authorized resources.
These principles reduce attack surfaces while strengthening visibility across digital infrastructures. Multiple layers of verification create a resilient system capable of detecting suspicious activities before significant damage occurs.
4. Identity Authentication as the Primary Security Layer
Identity authentication plays a central role in Zero Trust architecture. Every access attempt requires confirmation that the requester is legitimate. Advanced verification systems extend beyond simple passwords by incorporating multi-factor authentication techniques. These include biometric verification, hardware tokens, and one-time security codes delivered to trusted devices. Combining multiple authentication factors creates stronger protection against unauthorized entry. Additionally, adaptive authentication mechanisms analyze contextual signals such as login patterns, geographic locations, and device types. When irregular behavior appears, the system automatically demands additional verification steps, preventing potential intrusions.
5. Securing Endpoints and Establishing Device Trust
Devices serve as gateways to sensitive organizational resources, making endpoint security a critical component of Zero Trust strategies. Laptops, smartphones, and tablets often connect from diverse networks, increasing vulnerability to cyber threats. The Zero Trust Security Model evaluates device integrity before granting access. Security systems verify operating system updates, antivirus status, and compliance with security policies. Devices that fail these checks are denied entry automatically. Continuous endpoint monitoring also detects suspicious behavior such as unauthorized software installations or unusual data transfers. This proactive approach prevents compromised devices from becoming entry points for widespread network breaches.
6. Network Segmentation for Enhanced Threat Containment
Network segmentation divides digital infrastructures into smaller, controlled zones with distinct access permissions. This strategy limits the movement of attackers who manage to breach one segment. The Zero Trust Security Model enhances this concept through micro-segmentation, which applies highly granular security controls around applications and data sets. Each segment operates independently, requiring specific authorization for access. If a breach occurs, its impact remains confined to a limited area, preventing large-scale damage. Additionally, segmented environments improve threat detection by making unusual network traffic patterns easier to identify and investigate.
7. Limiting Exposure Through Least-Privilege Access
Least-privilege access ensures users receive only the permissions necessary for their responsibilities. Excessive access rights increase the risk of both accidental misuse and intentional exploitation. The Zero Trust Security Model enforces role-based access controls that clearly define authorization levels. Users cannot interact with resources beyond their assigned permissions. This disciplined approach restricts the potential damage caused by compromised accounts. Regular audits further strengthen protection by identifying and removing outdated privileges. By limiting unnecessary access, organizations reduce vulnerabilities while maintaining smooth operational workflows.
8. Continuous Surveillance for Proactive Threat Prevention
Real-time monitoring is essential for identifying and mitigating cyber threats before they escalate. The Zero Trust Security Model employs intelligent surveillance systems powered by artificial intelligence and behavioral analytics. These tools study normal activity patterns and detect deviations instantly. For instance, sudden high-volume data transfers or login attempts from unfamiliar regions trigger immediate alerts. Security teams can respond rapidly to investigate anomalies and neutralize risks. Continuous surveillance transforms cybersecurity into a proactive discipline that prevents incidents instead of merely reacting to them after damage occurs.
9. Strengthening Data Protection Through Encryption
Encryption protects sensitive information by converting it into unreadable formats that unauthorized users cannot interpret. The Zero Trust Security Model requires encryption for both stored data and information transmitted across networks. This ensures confidentiality even if cybercriminals intercept communications. Advanced encryption protocols safeguard financial records, intellectual property, customer data, and internal communications. Secure encryption also supports compliance with international data protection regulations. By embedding encryption across digital ecosystems, organizations add a powerful defense layer that complements authentication and access control mechanisms.
10. Enabling Secure Connectivity for Remote Workforces
Remote work environments introduce complex cybersecurity challenges as employees access systems from various locations and networks. The Zero Trust Security Model ensures secure connectivity by verifying every access request regardless of geographic origin. Secure gateways, identity authentication systems, and device compliance checks create a protected remote access framework. Employees can work productively without compromising organizational security standards. Centralized policy enforcement further simplifies management across distributed teams. Businesses benefit from operational flexibility while maintaining strong digital defenses against evolving cyber threats.
11. Strategic Advantages of Zero Trust Implementation
Organizations adopting the Zero Trust Security Model gain numerous strategic benefits beyond improved protection.
• Reduced likelihood of major data breaches
• Improved monitoring of user activities and system interactions
Additionally, businesses experience faster incident response, stronger compliance readiness, and enhanced customer trust. Lower recovery costs and minimized downtime contribute to long-term financial stability. This security framework also strengthens brand reputation by demonstrating commitment to safeguarding sensitive information.
12. Overcoming Challenges in Zero Trust Deployment
Transitioning to Zero Trust architecture requires careful planning and resource allocation. Legacy systems may lack compatibility with modern authentication technologies, necessitating infrastructure upgrades. Integration across multiple platforms can introduce technical complexity. Employees may also perceive additional verification steps as inconvenient. Organizations can address these obstacles through phased implementation strategies and cybersecurity awareness programs. Gradual deployment minimizes operational disruptions while ensuring employees adapt comfortably to new protocols. Clear communication about security benefits fosters cooperation and supports successful transformation.
13. Technologies Powering the Zero Trust Ecosystem
A variety of advanced technologies enable effective Zero Trust implementation. Identity and Access Management platforms oversee authentication and authorization processes. Multi-factor authentication tools provide layered identity verification. Endpoint Detection and Response systems continuously monitor device behavior for suspicious activity. Secure Access Service Edge frameworks integrate networking and security services into unified cloud-based solutions. Artificial intelligence enhances threat detection by analyzing large volumes of data rapidly. When integrated effectively, these technologies form a comprehensive ecosystem that validates every access request and strengthens digital resilience.
14. The Future Landscape of Zero Trust Cybersecurity
Emerging technologies such as artificial intelligence, cloud-native platforms, and Internet of Things ecosystems continue reshaping digital infrastructures. These advancements introduce new vulnerabilities that traditional security models cannot address efficiently. The Zero Trust Security Model offers a flexible foundation capable of adapting to evolving risks. Continuous authentication mechanisms, granular authorization controls, and intelligent monitoring systems ensure scalable protection. As cyber threats grow increasingly sophisticated, Zero Trust principles will become central to global cybersecurity strategies. Organizations embracing this model today prepare themselves for a safer and more resilient digital future.
Conclusion
The evolving digital environment demands cybersecurity strategies that move beyond outdated trust assumptions. The Zero Trust Security Model establishes a proactive defense system based on continuous verification and strict access governance. Users, devices, and applications must demonstrate legitimacy before accessing sensitive resources. Through strong identity authentication, endpoint protection, network segmentation, encryption, and real-time monitoring, organizations create multiple layers of intelligent defense. Although implementation requires investment and structured planning, long-term advantages significantly outweigh initial challenges. Businesses benefit from reduced breach risks, improved compliance readiness, enhanced operational visibility, and greater resilience against sophisticated attacks. As remote work expands and cloud adoption accelerates, Zero Trust becomes a vital framework for modern cybersecurity. Organizations that adopt this forward-thinking approach strengthen stakeholder confidence and secure their digital assets effectively in an increasingly connected world.
